
Portals made specifically for your patients offer data security that email never could.
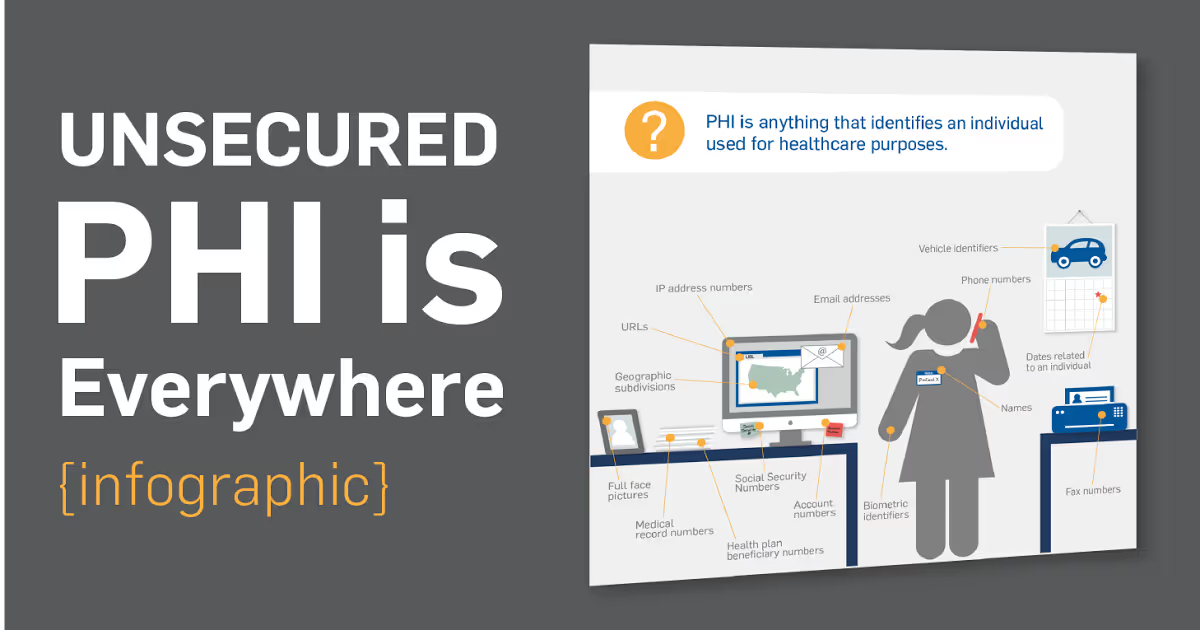
The unprotected PHI problem is easy to fix, but it must start with you.
Once you have established that your records reflect reality, it is time to monitor to ensure they are accurate.
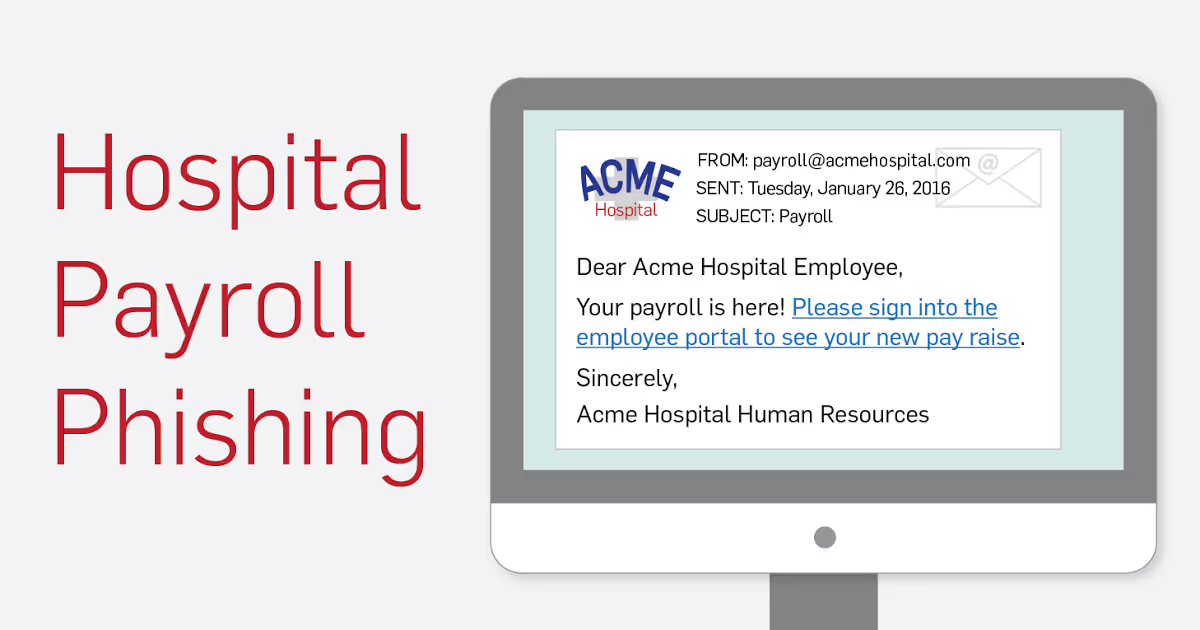
Essentially, the hackers steal paychecks from right under their noses.

My advice? Decide to take security seriously.

How to find the risks you might be missing.
Vulnerability scanning is one of the only crucial things that can help companies keep up-to-date on emerging vulnerabilities.
Visa requires annual validation of PCI compliance.

See what changes your payment application vendor should make.
When it comes to finding security weaknesses in your business, vulnerability scanning is a great place to start.

PCI 3.2 has come out with new requirements for penetration testing and network segmentation.

Learn more information about the Shoplift Bug, how it makes your system vulnerable, and what you need to do to combat it.

Here's what you need to know about the supplemental guide for scoping and network segmentation.

Learn what PCI scope categories your systems fall into.

MFA is an additional layer of security you should apply to all of your sensitive data.

For some preventative measures, back up your files regularly and keep your anti-virus software up to date.

PCI requirement 9 is all about physical security.

Start 2018 with our top blogs to help you with your data security and compliance efforts.

PCI advice for new ISOs. Here are three tips to help Independent Sales Organizations (ISOs) better position their PCI program

More often than not, data breaches are the result of an attack that takes advantage of our inattention and naiveté: social engineering.

SecurityMetrics PIIscan helps you find unencrypted data and comply with security mandates.