
The EU General Data Protection Regulation (GDPR) will come into effect on May 25, 2018.

Payment Card Industry (PCI) compliance is required for any organization that takes payment cards.
Maintaining HIPAA compliant passwords is a key step towards protecting ePHI.
HIPAA includes many such acronyms, mostly security-related.
Don’t forget to document every HIPAA compliance effort as evidence to present to the OCR if your entity is chosen for auditing.

Make the simple change to require unique usernames and passwords on the network level for each one of your staff members.

If you’re not sure what your HIE should be doing, have a look at ONC’s health IT security resources.
Either manage your business associate security or prepare for a data breach.

You can’t afford to be passive anymore; it’s time to be aggressive.
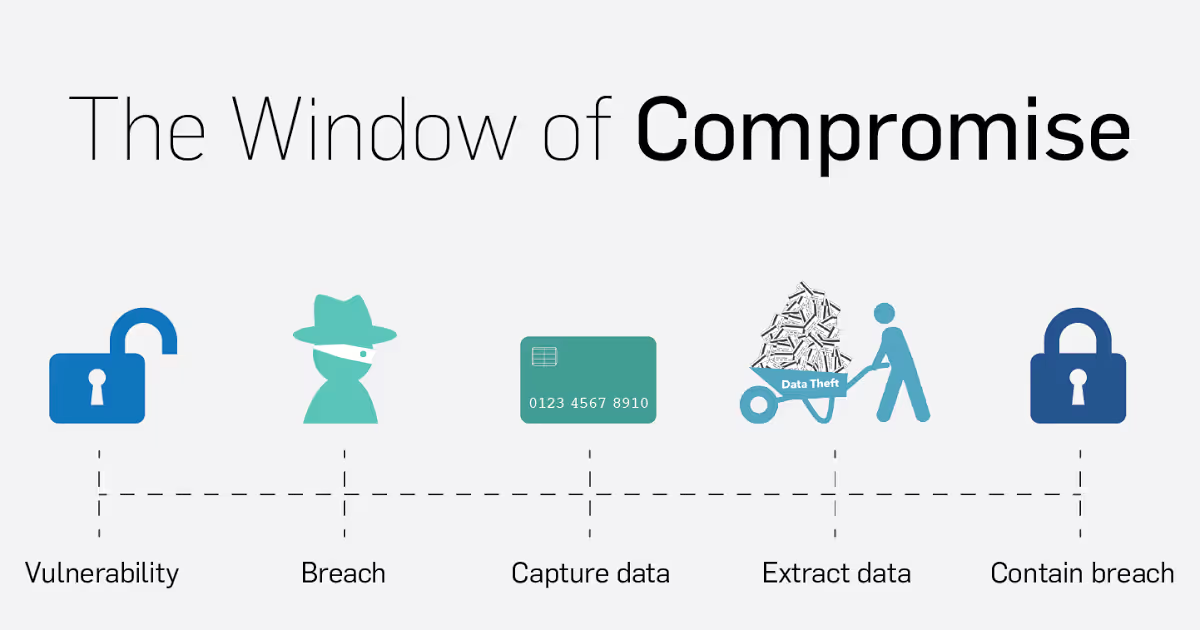
On average, a merchant was vulnerable for 470 days before an attacker was able to compromise the system.

See what changes PCI 3.2 brings and what you’ll need to do.
Learn what’s involved in the Phase 2 HIPAA Audit Program and how you can prepare.

Network security is more crucial than ever for healthcare providers.
HIPAA Compliance in “the cloud” Cloud data storage is a common and convenient option for healthcare organizations.
The best way to inspire better security practices is to show examples of true security blunders.

What happens when forensic investigators can’t find evidence of a compromise?

Hackers are getting smarter than our automated detection tools.
Hopefully, you'll realize some actions you should take to ensure your own business’ security.
Front desk clerks are friendly…sometimes to a fault, but friendly doesn’t necessarily equal secure.

The HHS says shredding, burning, pulping, and pulverizing are the only way these records should be destroyed.

Can customer service and front desk security co-exist?

Some falsely assume because mobile devices are technologically advanced and marketed as ‘secure’, PHI will automatically be protected.

To help further the fight against fraudsters and data thieves, the SecurityMetrics Forensic Investigation team has identified several common attack types associated with recent breaches.